In 2024, the average cost of a data breach in Germany reached 4.9 million euros. Yet most organizations still treat security as a final checkpoint—something to verify before release. This approach is fundamentally broken. By the time you find vulnerabilities at the end of the pipeline, fixing them is expensive, disruptive, and often too late.
Why Traditional Security Models Fail
The old model was simple: developers build, operations deploy, and security reviews at the end. But in a world of weekly (or daily) releases, this creates an impossible bottleneck. Security teams cannot review code fast enough. Developers resent the delays. And when pressure mounts, security reviews get shortened or skipped entirely.
Security that slows delivery will be bypassed. Security that accelerates delivery will be embraced.
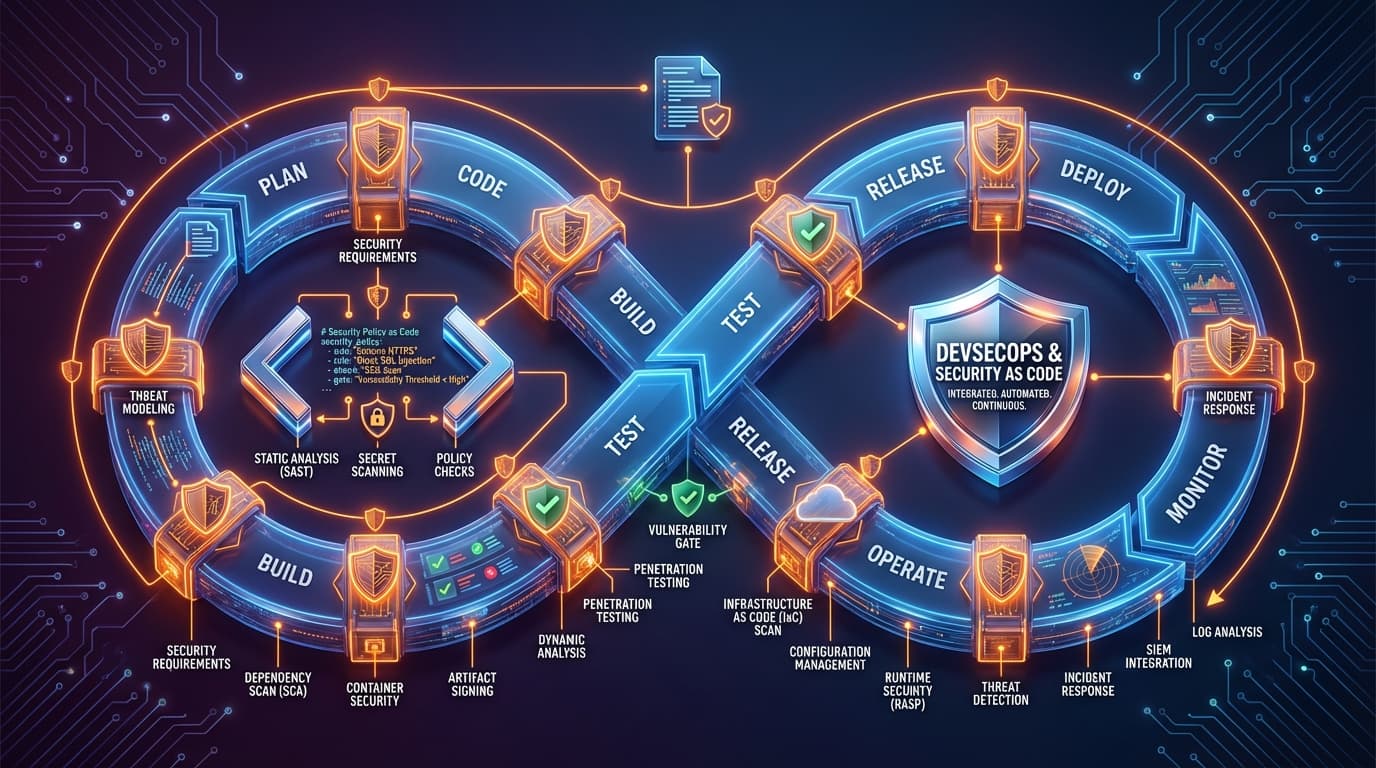
DevSecOps solves this by embedding security into every stage of the development lifecycle. Security becomes code—automated, version-controlled, and tested just like application code.
The Four Pillars of Security as Code
1. Policy as Code
Security policies should not live in PDF documents that nobody reads. They belong in code repositories, enforced automatically. Tools like Open Policy Agent (OPA), Kyverno, and HashiCorp Sentinel let you define policies that are version-controlled, testable, and automatically enforced.
For DACH enterprises navigating GDPR, NIS2, and industry-specific regulations, policy as code is transformative. Compliance becomes auditable and provable, not a checkbox exercise.
2. Infrastructure as Code Security
When your infrastructure is defined in Terraform, CloudFormation, or Pulumi, you can scan it before deployment. Tools like Checkov, tfsec, and Trivy analyze your infrastructure code for misconfigurations—exposed S3 buckets, overly permissive IAM roles, unencrypted databases.
The key insight: catching these issues in a pull request is 100x cheaper than finding them in production.
3. Pipeline Security Integration
Every stage of your CI/CD pipeline should include security checks:
- Code commit: Secret scanning, pre-commit hooks for sensitive data
- Build: Static Application Security Testing (SAST), dependency vulnerability scanning
- Container build: Image scanning, base image verification
- Deploy: Dynamic Application Security Testing (DAST), infrastructure validation
- Runtime: Continuous monitoring, anomaly detection
4. Secrets Management
Hard-coded secrets remain one of the most common security failures. Modern DevSecOps requires proper secrets management: HashiCorp Vault, AWS Secrets Manager, Azure Key Vault, or similar solutions. Secrets should be injected at runtime, rotated automatically, and never appear in code or logs.
Implementing DevSecOps Without Slowing Down
The fear is always the same: "Security checks will slow our pipeline." This fear is valid—poorly implemented security absolutely destroys velocity. Here is how to avoid that trap:
Optimize for Speed
- Parallelize scans: Run SAST, DAST, and dependency checks concurrently
- Cache results: Do not rescan unchanged components
- Prioritize findings: Block on critical issues, warn on medium, log low
- Use incremental scanning: Only scan changed code, not the entire codebase
Reduce False Positives
Nothing kills developer trust faster than false alarms. Tune your tools aggressively. Maintain allowlists. Review and adjust thresholds regularly. A scanner that cries wolf gets ignored.
Provide Developer Self-Service
Developers should be able to run security scans locally before pushing code. Provide them with the same tools the pipeline uses. When developers can fix issues before they reach CI, everyone wins.
Compliance as Code for EU Regulations
DACH enterprises face a complex regulatory landscape: GDPR, NIS2, the Digital Operational Resilience Act (DORA), and sector-specific requirements. DevSecOps transforms compliance from a periodic audit nightmare into continuous assurance.
- Automated evidence collection: Every pipeline run generates audit trails
- Continuous compliance validation: Policies are checked on every change
- Drift detection: Unauthorized changes are flagged immediately
- Reproducible environments: Infrastructure as code ensures consistency
Starting Your DevSecOps Journey
You do not need to implement everything at once. Start with these high-impact, low-friction steps:
- Add dependency scanning: Tools like Dependabot, Renovate, or Snyk identify vulnerable libraries with minimal configuration
- Implement secret scanning: GitLeaks, TruffleHog, or platform-native tools catch secrets before they reach the repository
- Scan infrastructure code: Add Checkov or tfsec to your Terraform workflow
- Establish security champions: Embed security-minded developers in each team
The Cultural Shift
Tools are necessary but not sufficient. DevSecOps requires a cultural shift where security is everyone's responsibility. This means:
- Security training for developers: Not annual checkbox training, but practical, hands-on learning
- Blameless security postmortems: Learning from incidents without finger-pointing
- Shared metrics: Security teams measured on enablement, not just blocking
- Open communication: Developers should feel safe asking security questions
The organizations that treat security as a shared responsibility—not a separate team's problem—will be the ones that ship fast and stay secure. In 2026, security as code is not optional. It is how resilient organizations operate.